Center for
Information Technology Integration
First Steganographic Image in the Wild
October 12th, 2001:
Niels Provos and
Peter Honeyman,
computer scientists at the University of Michigan's Center for Information
Technology Integration, are searching for steganography on the
Internet. After a month of downloading two million images from
eBay auctions with over sixty workstations computing secret keys
for images, no hidden messages could be found.
This week, the first steganographic image in the wild was
found due to an ABC coverage
of steganography. During the ABC coverage, an image called
"sovereigntime.jpg" was shown. It was supposed to have an image
of a B-52 bomber plane as steganographic content.
Using the Steganographic
Detection Framework developed by Niels Provos, it
is very easy to retrieve the hidden message from the ABC image.
It takes only a second to identify the image as likely
carrier of steganographic information and to find the secret key
that is required to extract thie hidden message. It is not too
much of a suprise that the secret key turns out to be abc.
Cover Image

|
|
Original Image from ABC
-
During the broadcast, an internet security consultant
displayed a jpeg image,
shown on the left.
-
He asserts that it contains a hidden image of a B52.
-
The broadcast showed fabricated images that were
suggesting terrorist use of steganography. In fact, it
was just a demonstration.
-
Read about it in a posting on the Politech
list or in an article
by Duncan Campbell in Telepolis.
|
|
|
Hidden Message
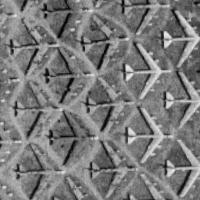
|
|
Steganographic Detection Framework in Action
-
The following demonstrates the use of the Steganography
Detection Framework:
$ stegdetect sovereigntime.jpg
sovereigntime.jpg : jsteg(***)
$ stegbreak -tj -f wordlist sovereigntime.jpg
Loaded 1 files...
sovereigntime.jpg : jsteg(abc)
Processed 1 files, found 1 embeddings.
Time: 1 seconds: Cracks: 1156, 1156.0 c/s
-
Stegdetect shows that there might be hidden information
inserted by the JSteg tool.
-
Stegbreak verifies that a hidden message exists.
The secret key to extract the hidden message is "abc."
-
The hidden message turns out to be an image. It is
displayed on the left.
-
The image shows an aerial view of the "B-52 graveyard" at
Davis-Monthan Air Force Base. Available via Terraserver.
|
For further questions, please check the Steganography
Press Information or contact Niels Provos <provos@citi.umich.edu>.
Niels Provos
Last modified: Fri Oct 12 19:17:05 EDT 2001